For all of the conveniences and wonder that additive manufacturing has provided within the past few years thanks to the desktop 3D printer revolution, the variety of processes used to create these millions of objects have oftentimes been more fascinating than the resulting 3D printed objects themselves.
Among other reasons, smartphone apps and 3D scanners have significantly lowered the barrier to entry for creating physical objects. Although CAD software such as SolidWorks or Fusion 360 is still needed to produce more polished designs with engineering details and manufacturing in mind, it’s been pretty incredible to see what people have been able to create without these traditional object creation tools.
Now, this ease of hardware creation – combined with the open source nature of 3D printing – is proving to be a headache (and a lesson in physical security) for the TSA after The Washington Post recently published a photo of the TSA’s set of master luggage keys.
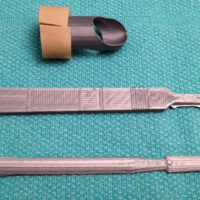
Unsurprisingly, a group of lock-picking and security enthusiasts saw this as a ripe opportunity for a challenge – and successfully reproduced the keys using a 3D printer.
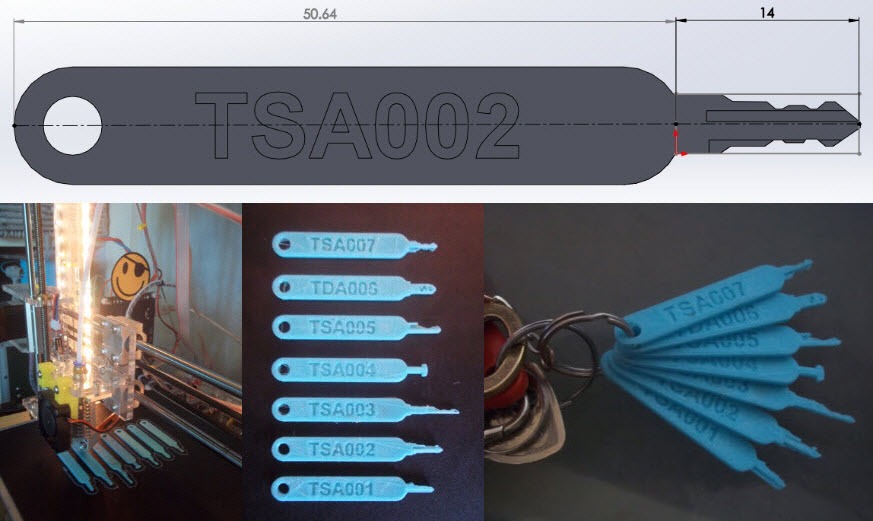
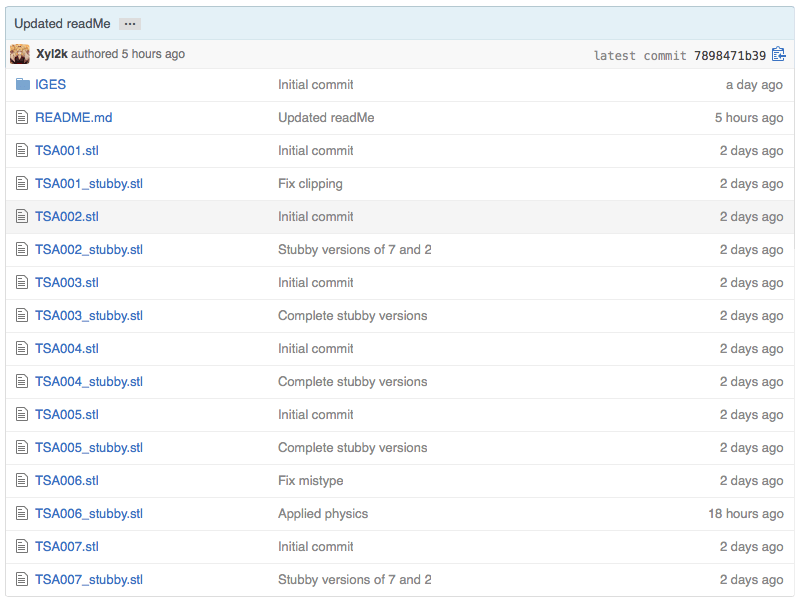
The keys – which the TSA uses to open a variety of locks – are now freely available to anybody with a 3D printer now that the resulting STL files for the key set have been uploaded to GitHub.
Of course, it would be easy to write this all off as hype, except that at least one person has posted a video showing that the keys do in fact open common locks:
OMG, it's actually working!!! pic.twitter.com/rotJPJqjTg
— Bernard Bolduc (@bernard) September 9, 2015
“People need to be aware that even though someone says ‘use these approved locks,’ don’t take their word for it,” says Shahab Sheikhzadeh, a New Jersey-based security researcher.
“We’re in a day and age when pretty much anything can be reproduced with a photograph, a 3-D printer and some ingenuity.”
According to the GitHub uploader, the release of the master key files is meant to prove to anyone who uses the TSA-approved locks that they should no longer expect them to offer much security. Of course, this wouldn’t be the case if they hadn’t decoded the master key in the first place – but the key takeaway here is that this could happen with anything, anytime – if somebody was motivated enough.